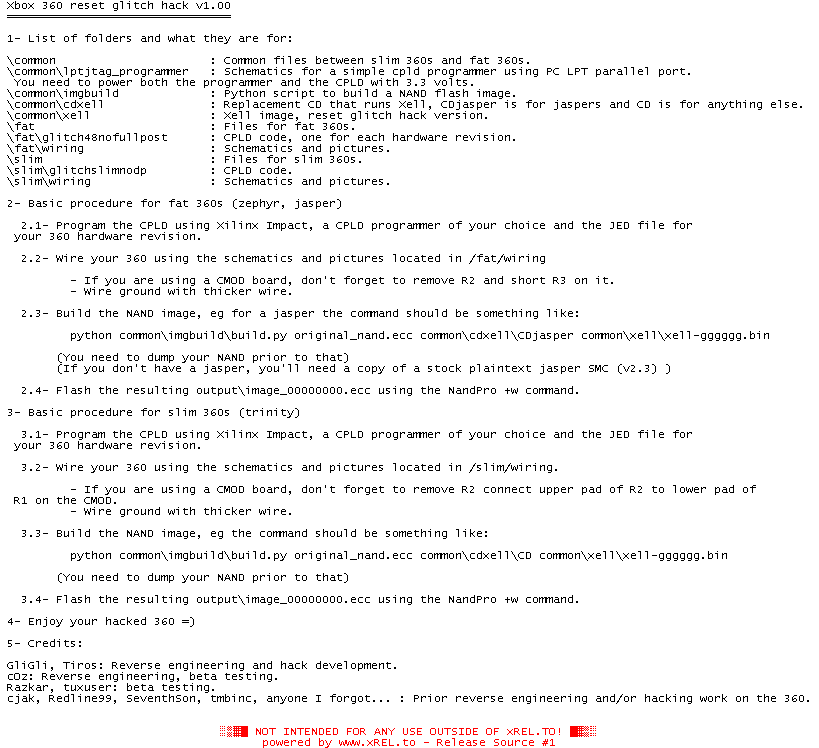
Xbox 360 reset glitch hack v1.00
1- List of folders and what they are for:
\common : Common files between slim 360s and fat 360s.
\common\lptjtag_programmer : Schematics for a simple cpld programmer using PC LPT parallel port.
You need to power both the programmer and the CPLD with 3.3 volts.
\common\imgbuild : Python script to build a NAND flash image.
\common\cdxell : Replacement CD that runs Xell, CDjasper is for jaspers and CD is for anything else.
\common\xell : Xell image, reset glitch hack version.
\fat : Files for fat 360s.
\fat\glitch48nofullpost : CPLD code, one for each hardware revision.
\fat\wiring : Schematics and pictures.
\slim : Files for slim 360s.
\slim\glitchslimnodp : CPLD code.
\slim\wiring : Schematics and pictures.
2- Basic procedure for fat 360s (zephyr, jasper)
2.1- Program the CPLD using Xilinx Impact, a CPLD programmer of your choice and the JED file for
your 360 hardware revision.
2.2- Wire your 360 using the schematics and pictures located in /fat/wiring
- If you are using a CMOD board, don't forget to remove R2 and short R3 on it.
- Wire ground with thicker wire.
2.3- Build the NAND image, eg for a jasper the command should be something like:
python common\imgbuild\build.py original_nand.ecc common\cdxell\CDjasper common\xell\xell-gggggg.bin
(You need to dump your NAND prior to that)
(If you don't have a jasper, you'll need a copy of a stock plaintext jasper SMC (v2.3) )
2.4- Flash the resulting output\image_00000000.ecc using the NandPro +w command.
3- Basic procedure for slim 360s (trinity)
3.1- Program the CPLD using Xilinx Impact, a CPLD programmer of your choice and the JED file for
your 360 hardware revision.
3.2- Wire your 360 using the schematics and pictures located in /slim/wiring.
- If you are using a CMOD board, don't forget to remove R2 connect upper pad of R2 to lower pad of
R1 on the CMOD.
- Wire ground with thicker wire.
3.3- Build the NAND image, eg the command should be something like:
python common\imgbuild\build.py original_nand.ecc common\cdxell\CD common\xell\xell-gggggg.bin
(You need to dump your NAND prior to that)
3.4- Flash the resulting output\image_00000000.ecc using the NandPro +w command.
4- Enjoy your hacked 360 =)
5- Credits:
GliGli, Tiros: Reverse engineering and hack development.
cOz: Reverse engineering, beta testing.
Razkar, tuxuser: beta testing.
cjak, Redline99, SeventhSon, tmbinc, anyone I forgot... : Prior reverse engineering and/or hacking work on the 360.
![]() Registrierte Benutzer können Text-, Hintergrund- und ANSI-Art-Farbe individuell anpassen!
Registrierte Benutzer können Text-, Hintergrund- und ANSI-Art-Farbe individuell anpassen!